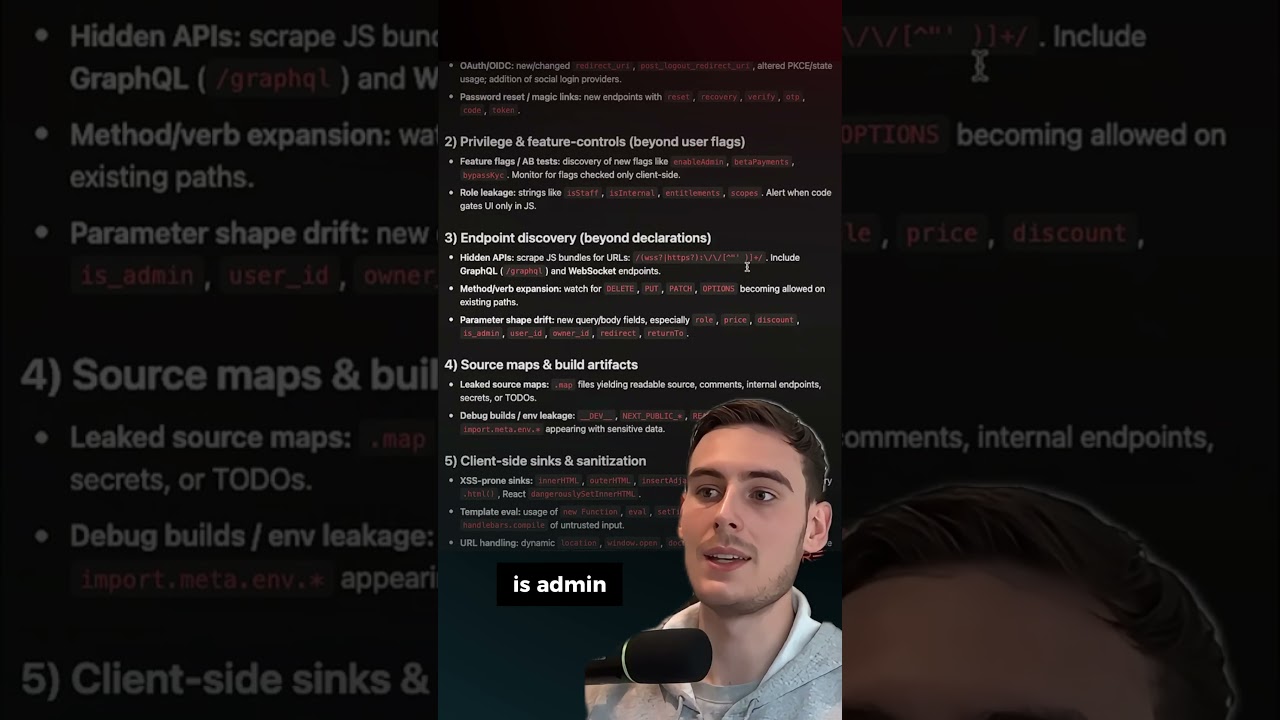
$300k Meta Client-Side Bugs + 10hr Marathon Hack-Along Recap (Ep. 158)
Episode 158: In this episode of Critical Thinking - Bug Bounty Podcast we talk about our personal takeaways from the CTBB Charity Hackalong, and then break down some InsertScript POCs, what a $55,000 bug can look like, and if Smart People Ever Say They’re Smart. Follow us on twitter at:…